Bitcoin vs. Quantum: FUD or Autoimmune Disease? - The Chopping Block
Speakers
Haseeb Qureshi
— Managing Partner, Dragonfly
Tarun Chitra
— Co-Founder & CEO, Gauntlet
Tom Schmidt
— General Partner, Dragonfly
Justin Drake
— Researcher at Ethereum Foundation
Summary
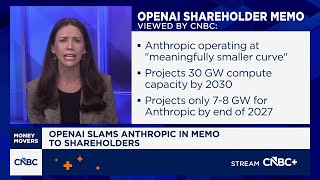
- Justin Drake co-authored a pivotal Google quantum paper showing a 20x improvement in Shor's algorithm, reducing qubits needed to break ECDSA to ~500k, pulling forward credible quantum attack timelines.
- Google's internal target for a post-quantum transition is now 2029, with Ethereum targeting the same date for its upgrade, though execution is more likely post-2030.
- Bitcoin faces a uniquely severe quantum threat: ~1/3 of its supply (including Satoshi's ~1M BTC) has exposed public keys, creating a massive political and economic dilemma on whether to burn or allow theft of these coins.
- Ethereum's quantum migration is technically harder due to ECDSA being embedded in smart contracts and admin keys, but its exposed asset percentage is an order of magnitude lower than Bitcoin's, allowing a potential "non-interventionist" property rights stance.
- The Bitcoin community's "FUD-denialist" culture is criticized as an "autoimmune disease" that risks downplaying a legitimate, solvable threat, in contrast to Ethereum's proactive, collaborative stance with groups like Blockstream.
- A sophisticated $285M hack on Solana's Drift protocol was a social engineering attack by North Korea (UNC4736), involving in-person trust-building over months and a malicious code repo, highlighting extreme vulnerability in admin key management.
- The emergence of Anthropic's "Mythos" AI model presents a near-term, catastrophic security threat, capable of finding critical vulnerabilities in all major software; its controlled release via "Project Glasswing" is a stopgap, not a solution.
- Formal verification of code is posited as the inevitable end-game for security, especially as AI makes bug-finding trivial; this could reduce client team sizes and potentially diminish the value of client diversity in favor of governance.
- A contrarian risk is raised that AI itself, via mathematical breakthrough, could break elliptic curve cryptography (ECDSA) before quantum computers do, adding urgency to post-quantum migration efforts.
Trade Ideas
Justin Drake states Ethereum has a proactive, collaborative strategy for quantum security, is working with other entities (like Blockstream) to build an industry standard, and has a target to upgrade all layers by 2029. This coordinated, technically advanced approach positions Ethereum as a leader in navigating the inevitable quantum threat, contrasting with denialism elsewhere. Ethereum's initiative and relative technical preparedness (e.g., lower percentage of immediately exposed assets vs. Bitcoin) make it a more resilient and attractive protocol in the face of a systemic cryptographic risk. The execution layer upgrade (smart contracts, admin keys) is a "Pandora's box" and could be botched or too slow.
Justin Drake criticizes Bitcoin's culture of "FUD denialism" regarding quantum as an "autoimmune disease," and highlights its uniquely large problem: ~1/3 of supply (incl. Satoshi's coins) has exposed keys, creating a severe political/fork dilemma. The combination of cultural resistance to addressing the threat and the massive, politically-charged remediation challenge creates significant downside risk and uncertainty. The quantum overhang presents a structural risk to Bitcoin's property rights narrative and stability that is more severe than for other chains, warranting caution. The quantum threat timeline slips far into the future, or the community successfully coordinates a fork/burn without major value destruction.
The Drift hack analysis reveals sophisticated, long-term social engineering by state actors (North Korea) targeting admin key security councils, and Justin Drake notes shockingly lax signing practices in other councils. Multi-sig admin keys are a critical centralized point of failure for many DeFi protocols, and they are being actively targeted by highly capable adversaries using novel, hard-to-defend attack vectors. The security model for protocol upgrades and admin controls in DeFi is currently inadequate against determined, sophisticated attackers, representing a systemic risk for the sector. Widespread adoption of formal verification, hardware security modules, and stricter operational security becomes standard practice quickly.
Up Next
This Unchained (Chopping Block) video, published April 10, 2026, features Justin Drake, Haseeb Qureshi discussing ETH, BTC, DEFI. 3 trade ideas extracted by AI with direction and confidence scoring.
Speakers: Justin Drake, Haseeb Qureshi · Tickers: ETH, BTC, DEFI